How to prevent csv injection in javascript
A practical, step-by-step guide to prevent csv injection in javascript with client-side validation, safe escaping, and server-side safeguards. Learn patterns, testing methods, and best practices for secure CSV exports in modern web apps.
You will learn how to prevent csv injection in javascript by applying practical validation, escaping, and safe CSV generation patterns. This guide covers client-side protections, common attacker vectors, and best practices for when to rely on server-side safeguards. Follow step-by-step actions for robust exports. We emphasize readability, maintainability, and compatibility across browsers, libraries, and data pipelines.
What CSV injection is and why it matters
When people ask how to prevent csv injection in javascript, they are usually trying to stop attackers from injecting formulas or dangerous content through simple CSV exports. An attacker can place characters like = or + in a data field, which, if opened in spreadsheet software, might execute unwanted calculations. The MyDataTables team emphasizes that the risk grows when CSVs travel through multiple layers: client-side forms, APIs, and downstream spreadsheets. Understanding where data enters and how it can be interpreted by Excel, Sheets, or other readers is the first step in building a robust defense. In practice, secure exports rely on validation, sanitization, and a cautious export strategy rather than relying on browser defaults or user habits. This article provides a practical plan for safeguarding your CSV flows while preserving usability and performance across browsers and libraries. According to MyDataTables, the easiest starting point is to treat every exported value as potentially dangerous and to encode risk signals at the boundary between your app and the user.
Client-side validation: what you can reasonably check
Client-side validation cannot be the sole defense, but it is a critical first line of defense for user experience and performance. Start by enforcing strict type checks and length limits on all fields before they enter the CSV. Reject or sanitize values that resemble formulas, such as strings starting with =, +, - or @, or those containing brackets and leading quotes that spreadsheets might interpret. Use whitelisting where feasible (e.g., allow only numbers, dates, and a safe subset of text) and provide clear error messages when data cannot be normalized. Remember that client-side controls must be complemented by server-side checks; clever users can bypass them, so you should not rely on them alone. Implement a centralized sanitizer function that is easy to audit and reuse across all export workflows. MyDataTables guidance highlights that consistent input handling minimizes surface area for injection.
- Validate inputs at the source (forms, API payloads) before any processing.
- Normalize data to simple, predictable formats when possible.
- Log and alert on unusual input patterns to detect attempted abuse.
Escaping and encoding: safe CSV generation patterns
The most reliable protection against CSV injection is to escape fields so that spreadsheet software cannot misinterpret data as formulas. A common strategy is to wrap every field in double quotes and to replace any internal double quotes with two double quotes. Some teams also prepend a harmless invisible character (e.g., a leading space or an apostrophe) to cells that could trigger formulas, but this should be used with care and documented for downstream users. When encoding, use a consistent charset such as UTF-8 and be mindful of BOM handling for Excel compatibility. If you export large datasets, consider streaming the CSV so you never hold unsafe data in memory. The MyDataTables approach recommends a canonical escaping routine that you can unit-test across datasets. Example patterns include: escaping internal quotes, wrapping fields, and avoiding unquoted dangerous prefixes.
Avoid dangerous formula injections: Excel and Sheets risk areas
Formula injection commonly occurs when a field begins with =, +, -, or @ and is interpreted by spreadsheet programs. To reduce risk, automatically prefix potentially dangerous cells with a non-evaluating character, or better yet, always escape and quote. For multi-valued cells, apply the same escaping logic, and ensure that engines used by your end users honor the same CSV format you generate. Be aware of regional CSV differences (semicolon vs comma delimiters) and encoding mismatches that could lead to misinterpretation. The safe pattern is consistent escaping and strict control over fields that could be executed as formulas. In practice, this means applying a definitive policy for all exported data, not only for high-risk fields.
Server-side generation vs client-side: when to lean on the backend
Client-side safeguards improve user experience, but server-side CSV generation is the gold standard for security. If possible, move the final CSV generation to a trusted back-end service where you can apply uniform validation, encoding, and access controls. On the server, you can enforce strict schema validation, use prepared patterns for escaping, and log export activity with user identifiers. When server-side generation is not feasible, implement a robust server-backed sanitizer layer that inspects data post-validation and before streaming the CSV. The MyDataTables team notes that combining client-side hygiene with server-side protections provides the strongest defense against injection and related CSV threats.
- Prefer server-side CSV generation for high-risk exports.
- If client-side export is required, ensure a strict sanitizer and a double-escaped policy.
Practical workflow: from data to safe CSV export
A practical workflow starts with data collection, followed by validation, sanitization, escaping, and encoding before writing to a CSV stream. Define clear schemas for every export path and implement a single, reusable exporter module that enforces the same rules across all pages and services. Use unit tests that cover edge cases, such as fields containing leading formulas, embedded quotes, or extremely long strings. Maintain documentation for developers and data stewards so everyone understands the export contract. The workflow should also include a verification pass that re-scans the generated CSV for suspicious patterns and confirms proper quoting and encoding. The goal is a predictable export that cannot be misused by spreadsheet readers.
Common pitfalls and how to test your exports
Common mistakes include skipping escaping for certain fields, inconsistent quoting, or assuming that any user-provided value is safe. Implement automated tests that simulate real-world inputs, including edge cases such as long strings, embedded newlines, and special characters. Test with different CSV dialects and with end-user spreadsheet applications to confirm compatibility. Use fuzz testing to uncover hidden injection vectors and maintain a regression suite to catch reintroductions of unsafe behavior. Finally, document test results and remediation steps so future changes remain safe. The MyDataTables guidance emphasizes that systematic testing and clear standards are the best defense against regressions.
Tools & Materials
- Code editor(Any modern editor (VSCode, WebStorm, Sublime).)
- Browser with dev tools(Chrome, Edge, or Firefox for debugging imports/exports.)
- CSV sample datasets(Include edge cases: quotes, newlines, long fields.)
- Validation library (optional)(e.g., validator.js for schema checks.)
- CSV generation utility or library(Use your own exporter or a trusted library with escaping support.)
- Test harness or unit tests(Jest, Vitest, or similar frameworks.)
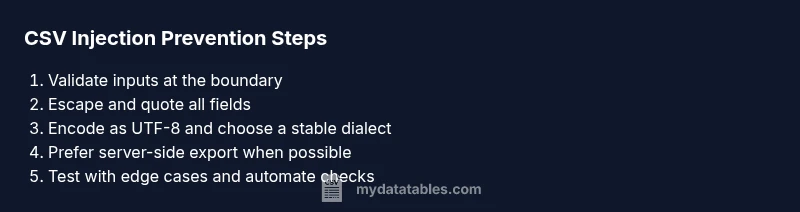
Steps
Estimated time: 30-60 minutes
- 1
Assess export data flow
Map every entry point where user data enters the CSV workflow. Identify fields that could trigger formulas and document export paths from UI to final file.
Tip: Create a data-map diagram to visualize entry points and risk fields. - 2
Validate inputs at the boundary
Enforce strict typing and schema validation at the API or form boundary. Reject or sanitize inputs that fail basic checks before processing.
Tip: Use a single source of truth for validation rules to avoid drift. - 3
Escape and quote every field
Wrap all fields in double quotes and escape internal quotes by doubling them. Ensure consistent quoting across all export paths.
Tip: Prefer a single escaping function used everywhere to avoid gaps. - 4
Use safe encoding and encoding-aware writers
Encode as UTF-8, handle BOM carefully for Excel, and pick a stable delimiter. Validate that the reader interprets the CSV correctly.
Tip: Test with regional dialects (comma vs semicolon) to ensure compatibility. - 5
Implement server-side fallback when possible
Perform final export on the server where you can enforce consistent validation and auditing. Provide a secure API for clients to request CSV exports.
Tip: Log export activity with user context to detect suspicious usage. - 6
Test, test, test
Run unit and integration tests that cover edge cases like formulas, long strings, and special characters. Validate that generated CSV files cannot be exploited when opened in readers like Excel or Sheets.
Tip: Automate end-to-end tests to catch regressions quickly.
People Also Ask
What is CSV injection and why is it dangerous?
CSV injection happens when data in a CSV can be interpreted as a formula by spreadsheet software. It can lead to unintended calculations or security risks. Preventing it requires consistent escaping, validation, and responsible export practices.
CSV injection occurs when data in a CSV is treated as a formula by spreadsheets, which can be dangerous. The fix is to escape, validate, and sanitize data before exporting.
Can client-side validation be trusted to secure CSV exports?
Client-side validation improves UX and catches obvious issues, but it should never be the sole defense. Attackers can bypass it. Always pair client-side checks with server-side validation and sanitized exports.
Client-side checks help users, but they aren't foolproof. Always add server-side validation and safe export patterns.
How should I escape fields in JavaScript for CSV?
Wrap each field in double quotes and double any internal quotes. This simple rule minimizes the risk of misinterpretation by spreadsheet readers and preserves data integrity.
Escape by quoting every field and doubling internal quotes to prevent formulas from being evaluated.
Is server-side CSV generation always better?
Server-side generation provides stronger security controls, auditing, and consistent encoding. It is recommended for high-risk exports, but client-side safeguards are still valuable for responsiveness.
Server-side CSV generation offers stronger protection and auditing, though client-side safeguards remain useful.
How do I test for CSV injection vulnerabilities?
Create test cases that include leading formulas, quotes, and long strings. Use automation to validate escaping, quoting consistency, and reader compatibility across multiple spreadsheet applications.
Test with edge cases like formulas and quotes, and automate checks for proper escaping and quoting.
What encoding should I use for CSV exports?
Use UTF-8 with a clear policy on BOM handling. Consistent encoding avoids character misinterpretation and ensures broader compatibility with Excel, Sheets, and other readers.
Stick to UTF-8 and handle BOMs consistently for cross-platform compatibility.
Should I warn downstream users about safe CSV export formats?
Yes. Provide documentation on how to handle escaped CSV fields and what to expect when opening files in different spreadsheet programs. Clear guidance reduces confusion and errors.
Provide downstream guidelines so users know how to handle escaped CSVs safely.
Watch Video
Main Points
- Validate inputs at the data boundary
- Escape and quote every CSV field
- Prefer server-side CSV generation when feasible
- Test exports against real-world spreadsheet readers